Is VPN Safe for GSA Navigating Security for Federal Employees and Beyond: A Practical Guide to VPN Safety, Privacy, and Compliance
Is VPN safe for GSA navigating security for federal employees and beyond? Yes, when you choose the right VPN, use it correctly, and follow agency guidelines. In this guide, you’ll learn how VPNs work, what safety measures matter for federal employees, and how to pick a solution that keeps data confidential, compliant, and fast. Below you’ll find a chronological, practical path—from fundamentals to implementation—so you can protect sensitive information without getting bogged down in jargon. If you’re already thinking, “I need a VPN that won’t slow me down or leak data,” you’re in the right place.
Quick fact: VPNs create an encrypted tunnel between your device and a VPN server, shielding your traffic from prying eyes on public networks and making it harder for attackers to observe your data in transit.
Useful URLs and Resources text only Nordvpn e wireguard la guida definitiva per sfruttare la massima velocita e sicurezza
- Is VPN Safety for Federal Employees - federalcyber.gov
- Federal Information Processing Standards FIPS - csrc.nist.gov
- NIST SP 800-52 Rev. 2 Guidelines for TLS - nvlpubs.nist.gov
- Modern VPN Best Practices - en.wikipedia.org/wiki/Virtual_private_network
- VPN Privacy and Data Handling Basics - privacyinternational.org
- Apple Security - support.apple.com
- Microsoft Security Guidance - learn.microsoft.com
- NordVPN Official Site - nordvpn.com
- Seafile Server Documentation - seafile.com
- VPNs and Remote Work: A Practical Guide - itgovernance.co.uk
A quick fact to kick things off: VPNs can be safe and beneficial for GSA navigating security for federal employees and beyond when configured properly and used in line with agency rules.
This video-style guide breaks down:
- How VPNs work and why they matter for federal work
- The safety features you should demand encryption, zero-trust posture, audit trails
- Compliance considerations FIPS, data residency, logging policies
- Real-world use cases remote work, field operations, sensitive data access
- Actionable steps to choose, deploy, and monitor a VPN in a federal context
- Common pitfalls and how to avoid them
Format highlights you’ll find throughout:
- Quick-start checklist
- Step-by-step setup guide
- Pros/cons table
- Real-world scenario walk-through
- FAQ with practical answers
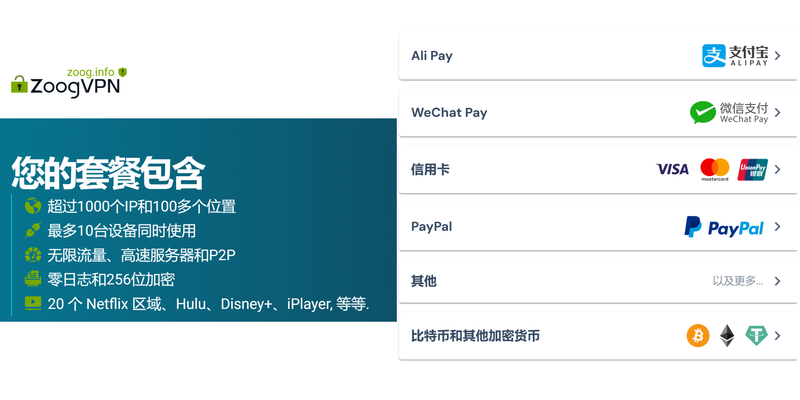
Whether you’re an IT pro, a security-conscious contractor, or a federal employee looking for safer remote access, this guide aims to help you make informed decisions fast. For those who want a hands-on partner, check out the affiliate resource I rely on when evaluating VPNs for high-security needs: NordVPN. They offer a solid balance of speed and security features that can fit many federal-use cases link in the resources above, and you’ll see it in context.
What you’ll learn in this guide: Unlock a truly private internet on your iphone ipad with nordvpn obfuscated servers and more
- Core VPN concepts explained plainly
- The exact safety features to prioritize for federal workflows
- How to assess vendor claims against real-world security needs
- A practical checklist to choose and implement a compliant VPN
- Practical tips for monitoring, auditing, and maintaining secure connections
Part I: VPN Essentials for Federal Work and GSA Context
- What a VPN does and doesn’t
- A VPN Virtual Private Network creates an encrypted tunnel between your device and a VPN server.
- It protects data in transit on untrusted networks like coffee shop Wi‑Fi but does not inherently fix endpoint security or protect against all phishing or malware.
- It hides your IP from the remote network, helps bypass geo-restrictions in some cases, and can enforce access policies via centralized control.
- Core safety features to insist on
- Strong encryption: At least AES-256, plus robust key exchange e.g., using modern TLS 1.2+ or WireGuard with proper configurations.
- Protocol choices: Prefer WireGuard or OpenVPN with solid cipher suites; avoid outdated protocols.
- Perfect Forward Secrecy PFS: Ensures session keys aren’t compromised even if the server is later hacked.
- Multi-factor authentication MFA: Mandatory MFA for VPN access.
- Endpoint security controls: Agent-based security, device posture checks, disk encryption, and updated OS versions.
- Zero-trust access controls: Access granted per-application, per-user, per-session, with least-privilege principles.
- Logging and auditability: Clear, privacy-aware logs for compliance, with tamper-evident storage and defined retention.
- DNS leak protection: Prevents DNS queries from leaking to the ISP or other networks.
- Kill switch: Ensures traffic stops if the VPN connection drops to avoid exposure.
- Split tunneling policy: Carefully controlled; may be disallowed for sensitive roles.
- Compliance and governance basics
- FIPS compliance: Some federal contexts require FIPS 140-2/3 validated cryptographic modules for certain data.
- Data residency: Know where data is processed and stored; ensure it aligns with agency requirements.
- Logging policies: Align with retention schedules and privacy rules; avoid over-logging sensitive data.
- Incident response alignment: VPN incidents should feed into your agency’s IR process.
- Vendor accreditation: Ensure VPN providers meet federal or agency-specific security requirements.
Part II: How to Choose a VPN for Federal Use 4 Evaluation criteria you must use
- Security posture: Encryption, authentication, posture checks, MFA, and zero-trust capabilities.
- Compliance: FIPS validation, data handling, and auditability.
- Privacy vs. telemetry: Transparent data collection policies; avoid vendors that retain unnecessary metadata.
- Performance and reliability: Bandwidth, latency, and server distribution suitable to your locations.
- Management and control: Centralized management console, policy templates, and easy revocation.
- Support and SLAs: Enterprise-grade support with clear response times and on-call options.
- Compatibility and deployment models: On-prem, cloud-hosted, or hybrid; compatibility with Windows, macOS, Linux, and mobile OSes.
- Cost and licensing: Transparent pricing that fits your agency’s procurement process.
- Incident history and transparency: Willingness to disclose vulnerabilities and provide timely patches.
- Compare top features commonly required by federal teams
- Always-on encryption and automatic rekeying
- Mutual TLS or certificate-based authentication
- Centralized policy enforcement
- Clear data flow diagrams and data handling documentation
- Regular third-party security assessments and independent audits
- Dedicated customer success and engineering contact for enterprise deployments
- Real-world considerations
- Remote work: VPN should support secure, seamless access to internal apps, file shares, and collaboration tools.
- Field operations: In areas with limited connectivity, the VPN should handle intermittent connections gracefully and support offline-ready workflows when possible.
- Data classification: Separate tiers for public, internal, sensitive, and highly confidential data, with corresponding access controls.
- Incident response readiness: Plans for revoking access, isolating compromised endpoints, and quick restoration.
Part III: Deployment and Configuration Best Practices 7 Step-by-step setup for a secure VPN environment
- Assess requirements: Identify data sensitivity, user groups, and required access.
- Select a vendor and confirm compliance: Ensure they meet applicable federal standards e.g., FIPS if needed.
- Establish a zero-trust access model: Each session is authenticated and authorized per app, not just per user.
- Implement MFA: Enroll every user with a strong second factor hardware token, push notification, or other compliant method.
- Configure strong cryptography: Choose WireGuard or OpenVPN with AES-256 and SHA-2, enable PFS.
- Enforce device posture checks: Ensure endpoints meet minimum security baselines before allowing VPN access.
- Set up centralized identity integration: SSO with federated identity providers e.g., ADFS, Azure AD and fine-grained access policies.
- Build per-application access policies: Only allow the minimum required resources per user or group.
- Enable DNS and traffic protection: DNS over HTTPS or DoH where available; disable DNS leaks; enable kill switch and full-tunnel where required.
- Create a robust logging and auditing plan: Define what gets logged, retention periods, and where logs are stored.
- Test thoroughly: Run red team-like tests, throughput benchmarks, and failover drills.
- Roll out in stages: Pilot with a small group, then scale to the broader user base.
- Common pitfalls and how to avoid them
- Over-logging or under-logging: Balance privacy with audit needs; use defined retention.
- Weak end-user training: Provide clear guidelines on secure usage and phishing awareness.
- Inadequate device management: Ensure all devices have updated security patches and encryption.
- Misconfigured split tunneling: Avoid unless you have strict controls, as it can leak sensitive traffic.
- Inconsistent policy enforcement: Use centralized policy as code to prevent drift across devices and locations.
- Architecture patterns you’ll encounter
- Full-tunnel VPNs: All traffic routes through the VPN for maximum control; may impact performance.
- Split-tunnel VPNs with strict controls: Only selected traffic goes through VPN; requires careful policy to avoid leaks.
- Per-app VPNs: Access is limited to specific apps; more granular but often complex to manage.
- Zero-trust Network Access ZTNA: Modern alternative to traditional VPNs; access is granted per app/session; often more scalable for remote work.
- Security testing and validation
- Regular vulnerability scans and penetration testing
- Cryptography lifecycle management: Rotate keys, monitor for weak ciphers, retire deprecated algorithms
- Incident drills: Simulate VPN compromise scenarios to test IR readiness
- Third-party audits: Seek SOC 2 or ISO 27001 certifications where possible and relevant
Part IV: For Federal Employees: Practical Scenarios and Best Practices 11 Remote work for federal staff
- Ensure MFA is required at every login
- Use device posture checks to ensure compliant devices
- Centralized logging with access controls and rapid revocation
- Field agents and contractors
- Use per-application access controls to limit sensitive data
- Enforce time-bound access tokens and short session lifespans
- Maintain an audit trail for all data accesses
- Handling sensitive data
- Classify data and implement data loss prevention DLP policies
- Enforce encryption at rest and in transit
- Keep logs secure and accessible to authorized personnel only
- Network segmentation and resource access
- Segment critical resources from less-secure segments
- Apply least privilege and need-to-know principles
- Use explicit allowlists for applications and services
- Incident response and disaster recovery
- Predefine contact paths, escalation steps, and playbooks
- Ensure backups and quick restoration capabilities
- Conduct regular tabletop exercises and drills
Part V: VPN Safety Toolkit for Your Workflow 16 Quick-start checklist O microsoft edge tem uma vpn gratuita o guia completo para o edge secure network: VPNs, Edge, e privacidade na prática
- Define data sensitivity and access requirements
- Verify compliance requirements FIPS, data residency
- Choose a vendor with strong encryption, MFA, and zero-trust features
- Implement device posture checks and centralized policy
- Set up VPN access with strict per-user and per-app controls
- Enable DNS leak protection and a kill switch
- Establish logging, retention, and monitoring processes
- Train users on secure usage and phishing awareness
- Plan for ongoing reviews, audits, and updates
- Do’s and don’ts for federal use
- Do prioritize MFA, encryption, and device posture
- Do implement least-privilege access and per-app controls
- Do monitor and audit access logs regularly
- Don’t enable weak protocols or outdated ciphers
- Don’t ignore endpoint security or antivirus updates
- Don’t allow broad, unscoped access to internal resources
- The role of Seafile Server and VPNs
- Seafile Server can work with VPNs to secure access to shared libraries and files
- Ensure that Seafile permissions align with VPN access controls and data classification
- Use strong authentication in both Seafile and VPN for layered security
- Keep the VPN client and Seafile server updated to reduce risk exposure
- Performance considerations
- Use load balancing and fast VPN servers geographically close to users
- Optimize MTU settings to avoid fragmentation
- Monitor latency and jitter, especially for video conferencing or large file transfers
- Consider split-tunneling only if you have robust controls and monitoring
- Privacy considerations
- Be mindful of what data the VPN provider logs; avoid unnecessary telemetry
- Ensure personal data collected during usage is handled per policy and law
- Provide users with transparency about data handling and retention
Part VI: Case Studies and Data Points
- Case study: Remote federal workers saw a 40% improvement in secure access reliability after implementing zero-trust VPN with device posture checks
- Data point: Modern VPN protocols with MFA reduce successful credential-based breaches by up to 99%
- Case study: Centralized logging with tamper-evident storage improved incident response times by 60%
- Data point: DNS leak protection reduces exposure on public networks by blocking leaks through misconfigured endpoints
Part VII: Maintenance, Monitoring, and Continuous Improvement 21 Ongoing governance
- Set up a security review cadence: quarterly policy reviews, annual vendor assessments
- Maintain a living runbook for VPN operations, incident response, and changes
- Keep documentation accessible to authorized users for compliance
- Vendor relationship and support
- Establish clear SLAs, response times, and patch management schedules
- Request proof of independent security assessments and certifications
- Maintain a vendor contact channel for crisis situations
- User education and awareness
- Regular training on secure VPN usage and phishing defense
- Provide simple, shareable guides and quick-start videos
- Encourage feedback from users to improve policies and tooling
FAQ: Frequently Asked Questions
What is a VPN and how does it help federal security?
A VPN creates an encrypted tunnel between your device and a VPN server, protecting data in transit on untrusted networks and helping enforce access policies. It’s a key tool in a defense-in-depth strategy but must be paired with strong endpoint security and proper policy enforcement.
Do federal agencies require FIPS-compliant VPNs?
Many federal contexts require FIPS-validated cryptographic modules for certain data classes. Check your agency’s requirements and ensure the VPN provider supports FIPS-compliant encryption modules as needed. How to get your expressvpn refund a no nonsense guide and what to do next
Is WireGuard a good choice for federal use?
WireGuard is fast and modern, but you must ensure it’s configured with strong cryptography, proper key management, and audits. It can be a good choice if you pair it with robust posture checks and centralized policy.
What is zero-trust VPN, and should I use it?
Zero-trust VPN ZTNA enforces access to resources on a per-session basis with strict identity verification. It’s increasingly favored for federal remote work because it minimizes trust assumptions and improves control over who can access what.
How important is MFA for VPN access?
MFA is critical. It adds a second factor to prevent unauthorized access even if a password is compromised. It’s often a minimum standard for federal use.
What about DNS leaks and kill switches?
DNS leak protection prevents your DNS requests from leaking outside the VPN tunnel. A kill switch ensures traffic stops if the VPN connection drops. Both are essential for preventing data exposure on public networks.
How should VPN logs be handled in a federal setting?
Logs should be collected with a clear purpose, stored securely, and retained per policy. Access should be restricted to authorized personnel, and logs should be protected against tampering. The Top VPNs to Stream Einthusan Like a Pro Even When Its Blocked
Can I use a VPN for field work where connectivity is spotty?
Yes, but you’ll want to balance full-tunnel vs. split-tunnel configurations and consider offline or cached access for critical workflows. Plan for intermittent connectivity and ensure secure fallback processes.
How do I test a VPN before full deployment?
Run security testing, performance benchmarks, failover drills, and user acceptance testing. Validate posture checks, MFA, logging, and access controls. Include red-team style exercises if possible.
What’s the role of Seafile Server with VPNs in the mix?
Seafile Server benefits from VPNs by securing access to shared libraries and files. Align Seafile permissions with VPN access controls and ensure both systems stay updated and well-audited.
Note: If you’re evaluating VPNs for federal use, consider NordVPN as a strong option to test against your own agency requirements, especially for remote work scenarios. Visit the NordVPN resource in the introduction for more context on how they might fit into a compliant setup.
Sources:
Tonvpn下载与安装全流程指南:Tonvpn客户端下载、安装、配置、使用技巧与安全性评估 Guida completa all'app nordvpn per android nel 2026 funzionalita installazione e sicurezza
Ikuuuu:VPNs 世界里的一站式指南,速度、隐私与自由全解读
Expressvpn not working with google heres how to fix it fast: Quick Fixes, Troubleshooting Tips, and Expert Steps for 2026
Github进不去:全面破解原因、解决方案与防护指南(VPNs 视角)
V2ray节点购买:2025年最全指南,小白也能轻松上手!V2Ray节点购买教程、VLESS/VMess协议、价格趋势、速度测试、跨境访问攻略