How to generate openvpn ovpn files a step by step guide. A quick fact: generating OpenVPN .ovpn files is all about creating secure client profiles that can be imported into any OpenVPN client. In this guide you’ll get a step-by-step, easy-to-follow path to create, sign, and export VPN configuration files, plus practical tips to keep things secure. Here’s a compact rundown of what you’ll learn:
- What OpenVPN is and why .ovpn files matter
- How to set up your own Certificate Authority CA and server
- Step-by-step commands to generate client certificates and .ovpn profiles
- How to test and troubleshoot your VPN connections
- Common mistakes and best practices for security and scalability
If you’re new to this, don’t worry—I’ve broken everything into bite-sized steps and included tables, quick checklists, and example commands you can copy-paste. For extra help, you can check out additional resources at the end of this post. Quick links and resources: OpenVPN official docs, Easy-RSA guide, and general VPN best practices. Useful URLs and Resources: Apple Website - apple.com, OpenVPN Community - openvpn.net, Easy-RSA GitHub - github.com/OpenVPN/easy-rsa, Reddit VPN guide - reddit.com/r/VPN, OpenVPN Wiki - openvpn.net/wiki, Wikipedia VPN - en.wikipedia.org/wiki/Virtual_private_network, Data Security Standards - en.wikipedia.org/wiki/Data_security
Table of Contents
- Why generate OpenVPN .ovpn files
- Prerequisites and planning
- Step-by-step: set up a simple OpenVPN server and CA
- Step-by-step: create client certificates and .ovpn files
- Structure of an .ovpn file explained
- How to test your .ovpn profile
- Security best practices
- Troubleshooting common issues
- Real-world tips and optimization
- FAQ
Why generate OpenVPN .ovpn files
OpenVPN uses a single, portable client configuration file with embedded certificates and keys or references to them. The .ovpn file tells the client how to connect, which server to reach, what encryption to use, and how to verify the server. Having a ready-to-go .ovpn file for each client makes deployments fast, repeatable, and auditable.
Key benefits
- Portable and easy to distribute
- Centralized control over client credentials
- Works across major platforms Windows, macOS, Linux, iOS, Android
- Supports TLS authentication, modern ciphers, and compression controls
- Better audit trail when using a centralized CA
Prerequisites and planning
Before you start, map out your environment:
- Server with a public IP or domain
- OpenVPN server package installed Ubuntu/Debian, RHEL/CentOS, or others
- A Certificate Authority CA setup often via Easy-RSA
- Sane naming convention for clients e.g., user1, user2
- A plan for revocation and certificate management
Hardware and software checklist
- A dedicated server or VPS with at least 1 GB RAM for small setups; more for larger deployments
- OpenVPN software openvpn package
- Easy-RSA for CA and certificate management if not using a built-in CA
- A stable firewall rule set allow UDP/TCP on the chosen port, usually UDP 1194
- Optional: TLSAuth ta.key for an extra layer of security
Step-by-step: set up a simple OpenVPN server and CA
Note: This section uses Easy-RSA 3.x workflow, a common approach for generating CA and server keys. Securely accessing mount sinais network your guide to the mount sinai vpn
- Install OpenVPN and Easy-RSA
- Debian/Ubuntu:
- sudo apt-get update
- sudo apt-get install openvpn easy-rsa
- Debian/Ubuntu:
- sudo yum install epel-release
- sudo yum install openvpn easy-rsa
- Set up the CA and PKI directory
- make-cadir ~/openvpn-ca
- cd ~/openvpn-ca
- source vars
- ./clean-all optional
- ./build-ca
- Create a server certificate, key, and encryption files
- ./build-key-server server
- ./build-dh
- openvpn --genkey --secret keys/ta.key for TLSAuth
- Generate client certificate templates
- ./build-key clientname repeat for each client
- Copy the generated files to a secure location server side
- Create the OpenVPN server configuration
- Copy a sample config: sudo cp /usr/share/doc/openvpn/examples/sample-config-files/server.conf.gz /etc/openvpn/
- gunzip /etc/openvpn/server.conf.gz
- Edit /etc/openvpn/server.conf with:
- ca ca.crt
- cert server.crt
- key server.key
- dh dh2048.pem or dh2048.pem
- tls-auth ta.key 0
- server 10.8.0.0 255.255.255.0
- push "redirect-gateway def1 bypass-dhcp"
- push "dhcp-option DNS 8.8.8.8"
- user nobody
- group nogroup
- keepalive 10 120
- cipher AES-256-CBC
- auth SHA256
- compress stub-v2 optional
- persist-key
- persist-tun
- Enable IP forwarding and firewall rules
- sudo sysctl -w net.ipv4.ip_forward=1
- Update /etc/sysctl.conf to persist
- Set up firewall: allow UDP 1194 or your chosen port; set up NAT for VPN subnet
- Start and test the server
- sudo systemctl start openvpn@server
- sudo systemctl enable openvpn@server
- Check status: systemctl status openvpn@server
- Create a basic client config template we’ll embed into .ovpn later
Step-by-step: create client certificates and .ovpn files
- Generate a client certificate
- cd ~/openvpn-ca
- source vars
- ./build-key clientname
- Create a client .ovpn profile with embedded keys/certs
- You can generate a single .ovpn that contains the embedded CA, client cert, and client key
- Example template to paste into a new clientname.ovpn:
- client
- dev tun
- proto udp
- remote your-server-address 1194
- resolv-retry infinite
- nobind
- persist-key
- persist-tun
- remote-cert-tls server
- cipher AES-256-CBC
- auth SHA256
- key-direction 1
- verb 3
- -----BEGIN CERTIFICATE-----
- paste content of ca.crt
- -----END CERTIFICATE-----
- -----BEGIN CERTIFICATE-----
- paste content of clientname.crt
- -----END CERTIFICATE-----
- -----BEGIN PRIVATE KEY-----
- paste content of clientname.key
- -----END PRIVATE KEY-----
- -----BEGIN OpenVPN Static key V1-----
- paste content of ta.key
- -----END OpenVPN Static key V1-----
- Save as clientname.ovpn
- Transfer this .ovpn to the client device securely SFTP, scp, or a secure file share
- Ensure proper permissions so only the intended user can read it
Alternative: use inline certificates
- Instead of embedding, you can reference external certificate files with ca, cert, key entries, but embedding is more portable
Structure of an .ovpn file explained
- The header lines like client or dev tun configure the VPN client behavior
- The remote line points to your server address and port
- The ca, cert, key sections are the certificates and keys you’ve generated
- tls-auth if used improves security by adding a HMAC-based channel check
- cipher and auth specify encryption and hashing standards
- push directives are server-side preferences for clients
- The embedded sections
, , , are what make the .ovpn portable
How to test your .ovpn profile
- On Windows/macOS: install OpenVPN GUI/VPN client and import the .ovpn file
- On Linux: open a terminal and run:
- sudo openvpn --config clientname.ovpn
- Expected outcomes:
- A successful handshake and a connected VPN tunnel
- Verify routing with: ip route show 0.0.0.0/0
- Confirm DNS leaks are avoided by testing public DNS resolution
Quick testing steps
- ping 10.8.0.1 server VPN side
- curl ifconfig.me to verify public IP differs from your real IP
Security best practices
- Always use TLS 1.2 or higher and SHA256 or stronger for signatures
- Use a strong passphrase for private keys or protect them with restricted permissions
- Regularly rotate certificates and revoke compromised keys
- Keep the server OS and OpenVPN software up to date
- Consider using TLSAuth ta.key to prevent certain TLS attacks
- Enable firewall rules and limit access to the VPN server from trusted networks
- Use a dedicated VPN subnet that doesn’t clash with your internal network
- Consider enabling per-client certificates and revocation via a certificate revocation list CRL
Troubleshooting common issues
- Connection refuses or timeout
- Check server status and firewall rules
- Confirm the server is listening on the correct port
- Verify client config matches server’s port and protocol
- Certificate errors
- Ensure CA bundle matches on both server and client
- Confirm certificates haven’t expired
- DNS leaks
- Ensure push "dhcp-option DNS" lines point to reliable DNS servers
- Confirm the client is using the VPN DNS after connection
- Slow performance
- Check server CPU, bandwidth, and MTU settings
- Consider enabling compression only if you’re in a compatible environment
- Check network congestion and routing
Real-world tips and optimization
- Automate client provisioning with a script that generates .ovpn files with embedded certs
- Use a management plane for revocation and certificate tracking
- For mobile clients, prefer UDP for performance but keep fallback options
- If you’re behind NAT, you may need to use TCP or a different port, or set up a port-forward
- Monitor VPN usage and logs to catch misconfigurations early
- Consider split tunneling when appropriate to reduce load on the VPN
Frequently Asked Questions
How long does it take to generate a new client .ovpn file?
It typically takes a few minutes per client, depending on your familiarity and the size of your CA.
Can I embed certificates directly into the .ovpn file?
Yes, embedding certs and keys makes distribution easier; it’s common for portability and offline use.
What is the difference between UDP and TCP for OpenVPN?
UDP is generally faster and preferred for VPNs, while TCP can be more stable in networks with strict firewalls or NAT. Лучшие бесплатные vpn сервисы для iphone и ipad в 2026: обзор, сравнение и советы по безопасному выбору
How do I revoke a client certificate?
Use your CA management tool Easy-RSA to revoke the certificate and update the CRL on the server, then push updated CRLs to clients as needed.
What is TLSAuth ta.key and do I need it?
TLSAuth adds an extra HMAC layer to TLS handshake, improving security and blocking certain attacks. It’s recommended.
How do I test the connectivity from a client?
Install OpenVPN on the client, import the .ovpn, and connect. Verify IP, DNS, and route changes after connection.
Can I use a single server config for multiple clients?
Yes, you can reuse a server.conf and generate separate client certificates for each user to manage access individually.
What should I do if a client’s certificate is compromised?
Revoke the certificate in your CA, distribute a new certificate to the user, and invalidate the old one. Urban vpn para chrome 크롬에서 무료 vpn 사용법 완벽 가이드 2026년 업데이트: VPN 사용 팁과 실전 가이드
How do I add a second VPN server for load balancing?
Set up a second OpenVPN server with its own CA or a shared CA, distribute new client profiles for the second server, and use a DNS or VPN portal to direct traffic accordingly.
Are there performance considerations for large deployments?
Yes—monitor CPU, RAM, and VPN concurrency; consider separate subnets, multiple servers, and load balancing to scale.
Frequently Asked Questions
Q: What is the best practice for a secure OpenVPN setup?
A: Use a strong CA, rotate certificates, enable TLSAuth, enforce up-to-date ciphers, and tightly control access. Cisco AnyConnect VPN Cant Access The Internet Here’s How To Fix It: Quick, Clear Fixes You Can Try Today
Q: How do I avoid DNS leaks in OpenVPN?
A: Push a private DNS server option in server.conf and ensure clients use VPN DNS after connecting.
Q: Can I run OpenVPN behind a firewall?
A: Yes, but you may need to forward UDP 1194 or your chosen port and allow related traffic.
Q: Is it safer to embed credentials in the .ovpn file? How to download and install the nordvpn app on windows 11: A Practical Guide for VPN on Windows 11 or Nordic-Style Setup
A: Embedding makes distribution easier but requires strong file security. External references can be safer in some environments.
Q: What is the role of the CA in OpenVPN?
A: The CA signs server and client certificates, enabling trust and revocation management across your VPN.
Q: How often should I rotate keys and certificates?
A: Rotate periodically or upon compromise; enforce revocation of old certificates and reissue as needed. Softether vpn 클라이언트 완벽 가이드 무료 vpn 설정부터 활용법까지 2026년 최신: 실전 사용법, 설치 팁, 보안 이슈까지 한눈에 보는 완벽 가이드
Q: Can OpenVPN work on mobile devices?
A: Yes, OpenVPN is supported on iOS and Android with official apps and compatible .ovpn profiles.
Q: How do I secure the OpenVPN server itself?
A: Keep software updated, restrict firewall access, use strong authentication, and monitor logs.
Q: What are common file format pitfalls? Why Your iPhone VPN Keeps Connecting and How to Stop It
A: Ensure correct line endings, proper PEM formatting, and no stray spaces around certificate blocks.
Q: Where can I find official documentation for OpenVPN?
A: OpenVPN official docs at openvpn.net, and Easy-RSA guides on GitHub.
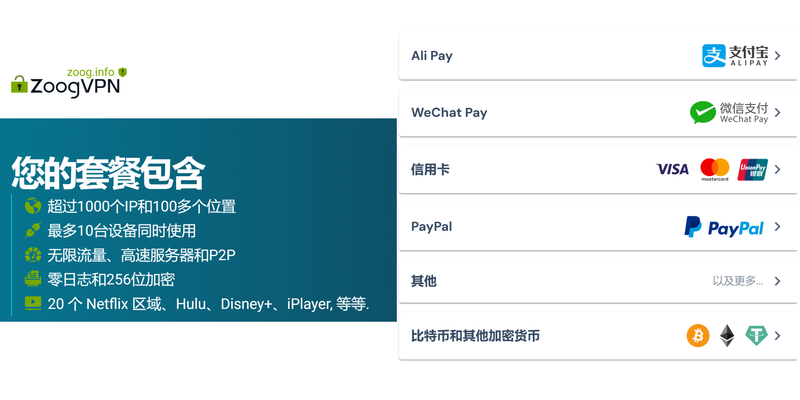
Affiliate note If you’re looking for a reliable privacy-friendly option to pair with your OpenVPN setup, consider a reputable VPN service. For quick navigation and added privacy features, you can explore options via the affiliate link below: NordVPN - Secure, fast, and easy VPN experience
End of Post Urban vpn proxy 다운로드 무료 vpn 설치부터 사용법 장단점까지 완벽 분석 2026년 최신 가이드
Sources:
免费手机vpn:全面对比与实用指南,选出最安全、最快的方案
加速器免費:2026 年免費網絡加速器與vpn 推薦與風險全解析,快速穩定的上網解法與風險剖析
How to Disable Microsoft Edge Via Group Policy GPO for Enterprise Management: Quick Guide, Tactics, and Best Practices
Ikuuuu官网:VPN 安全与隐私全攻略,提升上网自由与保护数据
便宜好用的vpn:实用指南、对比与选购要点 Globalprotect vpn connected but no internet heres how to fix it