Troubleshooting windows 11 forticlient vpn ipsec connection failures quickly? Here’s a concise, practical guide to get you back online. Quick fact: IPSec VPN issues on Windows 11 often come down to misconfigurations, certificate problems, or firewall blocks. This post walks you through a structured, easy-to-follow approach, with step-by-step actions, checklists, and real-world tips.
- Quick-start checklist: verify network, update FortiClient, check server status, and review credentials.
- Step-by-step guide: run through common failure modes, test connectivity, and apply fixes.
- Common formats you’ll find here: bullet lists for quick fixes, numbered steps for procedures, and tables for settings comparisons.
Useful resources you might want to reference (text-only links):
Apple Website - apple.com, Artificial Intelligence Wikipedia - en.wikipedia.org/wiki/Artificial_intelligence, Fortinet Support - support.fortinet.com, Windows 11 Help - support.microsoft.com, FortiClient VPN IPSec - docs.fortinet.com
Table of contents
- Why IPSec VPNs on Windows 11 fail
- Pre-flight checks
- Common failure modes and fixes
- Advanced troubleshooting steps
- Network and security considerations
- Client-side configuration tips
- Server-side considerations
- Optional optimisations and performance tips
- Real-world troubleshooting workflow
- FAQs
Why IPSec VPNs on Windows 11 fail
IPSec-based VPNs rely on a precise mix of configurations, certificates, and network paths. A small mismatch can break the entire tunnel. Some of the most common culprits include:
- Mismatched IPSec/IKE settings between client and server
- Expired or invalid certificates or pre-shared keys
- Firewall or NAT issues blocking IPSec/ESP/UDP ports
- DNS resolution problems or split tunneling misconfigurations
- Software conflicts, VPN profile corruption, or outdated FortiClient
- VPN server load, licensing, or policy blocks
Statistics and trends (recent years) show that user error and certificate problems account for a large share of failures, followed closely by port-blocking firewalls and outdated clients. Keeping Windows and FortiClient updated reduces many problems by a large margin.
Pre-flight checks
Before you start tearing things apart, do these quick checks:
- Check VPN server status: is the FortiGate/FortiProxy VPN service up and reachable?
- Confirm your user credentials: correct username, password, and any MFA codes.
- Ensure FortiClient is up to date: latest version often fixes IPSec quirks.
- Verify network connectivity: can you reach internal resources via another path? Is internet access stable?
- Review local firewall rules: Windows Defender Firewall and any third-party firewall should allow FortiClient and IPSec ports.
- Confirm time synchronization: certificate validation often fails if the client and server clocks drift.
Ports and protocols to verify:
- UDP 500 (IKE)
- UDP 4500 (NAT-T)
- ESP (protocol 50) and AH (protocol 51) depending on policy
- Some networks require UDP 1000+ or alternative ports for IPSec pass-through
Common failure modes and fixes
1) IPSec negotiation fails (IKE_AUTH_FAILED)
- Likely causes: bad credentials, certificate issues, or policy mismatch.
- Fix steps:
- Re-enter credentials; if MFA, ensure the token/app is syncing.
- Check certificate validity for both ends; install fresh client cert if required.
- Compare IKE phase 1 settings: encryption, hash, DH group, and lifetime with server policy.
- Enable verbose logging in FortiClient to capture IKE exchange details.
- Test with a different user profile to rule out account-specific problems.
2) VPN connects but no traffic (Tunnel established but no data)
- Likely causes: split tunneling misconfiguration, DNS issues, or firewall blocks.
- Fix steps:
- Verify route tables after connect: ensure the VPN network is present, and no conflicting routes exist.
- Check DNS settings: ensure DNS server provided by VPN is reachable.
- Disable split tunneling temporarily to confirm traffic routing.
- Check local firewall rules for outbound VPN traffic.
3) IPSec tunnel drops intermittently
- Likely causes: unstable network, aggressive MTUPath, or keepalive settings.
- Fix steps:
- Reduce MTU size on FortiClient or router to avoid fragmentation.
- Enable Dead Peer Detection (DPD) on both ends if supported.
- Monitor network stability with ping/trace routes to VPN gateway.
- Check for packet loss or jitter on the path.
4) Certificate validation errors
- Likely causes: expired certs, untrusted CA, or mismatched hostname.
- Fix steps:
- Confirm the server certificate is valid and not expired.
- Install the correct root and intermediate certificates in the Windows certificate store.
- Ensure the common name (CN) or SAN matches the server address you connect to.
- If using VPN profiles with embedded certs, re-import the profile.
5) MFA prompts hanging or failing
- Likely causes: time drift, push notification issues, or network congestion.
- Fix steps:
- Check device time and timezone settings.
- Ensure the MFA app is up to date and synced.
- Test with a backup method (SMS or token) if available.
- Review server-side MFA policy for block rules or throttling.
6) FortiClient VPN not starting after Windows update
- Likely causes: compatibility issues with the new Windows build.
- Fix steps:
- Ensure FortiClient supports your Windows 11 build; check Fortinet release notes.
- Reinstall FortiClient using the latest installer.
- Run FortiClient as administrator; disable compatibility mode if enabled.
- Check for conflicting VPN software and disable it.
7) DNS leaks or exposure
- Likely causes: VPN DNS not pushing or leaking when connected.
- Fix steps:
- Enable DNS over VPN if available; ensure VPN DNS servers are authoritative.
- Use a DNS leak test after connecting to validate.
8) NAT traversal issues
- Likely causes: NAT devices blocking ESP or UDP 4500.
- Fix steps:
- Enable NAT-T on both sides if supported.
- Confirm that UDP 4500 is open through any NAT devices.
- Consider using a different VPN protocol if IPSec with NAT-T is problematic (e.g., SSL/TRS VPNs) while keeping IPSec as a fallback.
9) Profile corruption or misconfiguration
- Likely causes: corrupted FortiClient profile or wrong config file.
- Fix steps:
- Delete the VPN profile and re-create it from scratch.
- Import a fresh profile from your IT team or FortiGate.
- Confirm all fields (server, port, VPN type, interface) match server expectations.
10) Time and date skew causing certificate errors
- Likely causes: clock drift by more than a few minutes.
- Fix steps:
- Make sure Windows Time is automatically synced.
- Sync with an NTP server and confirm timezone accuracy.
Advanced troubleshooting steps
- Enable detailed FortiClient logging:
- Go to FortiClient settings, enable verbose/diagnostic logs, and reproduce the issue. Review the log file for IKE_SA_INIT, IKE_AUTH, and CHILD_SA messages.
- Check Windows Event Viewer:
- Look for VPN-related events under Applications and Services Logs, and System logs for IPSec-related warnings.
- Use built-in Windows VPN diagnostic tools:
- Run: netsh advfirewall consec
- Run: netsh ipsec show config
- Verify certificate chain using MMC:
- Open MMC > Certificates > Local Computer > Personal/Trusted Root Certification Authorities.
- Test with a different device or OS version:
- If possible, test with Windows 10 or another device to isolate Windows 11-specific issues.
- Validate server policy:
- Confirm that gateway IP, tunnel name, and policy rules on the FortiGate align with the client profile.
- Check FortiGate logs:
- Look for rejected IKE_AUTH requests, certificate revocation list checks, or policy mismatches.
Network and security considerations
- Firewall rules: ensure that FortiClient and IPSec traffic are allowed both outbound and inbound on the client’s side, including NAT-T traffic.
- MTU and fragmentation: IPSec often struggles with too large packets; adjust MTU if necessary.
- VPN server health: busy gateways or licensing limits can cause timeouts or drops.
- Split tunneling vs full-tunnel: choose the appropriate mode for your use-case and security posture.
- DNS hygiene: ensure VPN-provided DNS is used to resolve internal domains; avoid leaking DNS queries.
Client-side configuration tips
- Keep FortiClient updated: new builds fix many known bugs.
- Use a clean VPN profile: re-create profiles rather than editing existing ones.
- Run as administrator when testing: some Windows settings require elevated privileges.
- Disable conflicting VPN software: some VPNs don’t play well together.
- Verify system time: NTP accuracy is crucial for certificate validity.
Server-side considerations
- Certificates and CA trust: ensure the root CA is trusted by clients and not expired.
- Policy alignment: IPSec encryption and integrity settings on the FortiGate must match client settings.
- NAT-T and firewall rules on the gateway: port allowances must align with client behavior.
- Licences and user policy: confirm the user has VPN access enabled and not throttled.
Optional optimisations and performance tips
- Minimise DNS leakage by forcing VPN-provided DNS for all traffic.
- Consider enabling split tunneling for non-critical traffic if security posture allows.
- Use QoS on the network to prioritise VPN traffic (especially on congested networks).
- Regularly refresh certificates and review validity periods to prevent sudden outages.
Real-world troubleshooting workflow
- Reproduce the issue and collect exact error messages.
- Verify network connectivity and firewall rules on the client.
- Confirm FortiClient version is current and the profile is correct.
- Check server health and logs; identify mismatches in policies or certs.
- Apply fixes in small, testable steps; re-test after each change.
- Document the final working configuration and steps for future reference.
Frequently Asked Questions
What is IPSec and how does it differ from SSL VPN?
IPSec is a suite of protocols for securing IP communications by authenticating and encrypting each IP packet in a data stream. SSL VPNs operate at the transport layer (TLS/SSL). IPSec often provides stronger network-level security for site-to-site or road-warrior VPNs, while SSL VPNs can be more flexible for application access through a browser. The Complete Guide to Uninstalling NordVPN Windows Mac
Why does my FortiClient VPN connect fail after a Windows 11 update?
Windows updates can alter network stack behavior, security policies, or certificate handling. Ensure FortiClient is fully updated, check compatibility notes, and re-create the VPN profile if needed.
How can I tell if the problem is client-side or server-side?
If other users on the same server can connect, the issue is likely client-side. If all users fail, the server or gateway is more likely the problem. Always check server logs first when available.
What settings should I verify on the FortiGate side?
IKE phase 1 settings (encryption, hash, DH group), IKE phase 2 (transform set), VPN user policies, certificate trust, NAT-T, and firewall policies allowing IPSec and ESP traffic.
Can I use a different VPN protocol to bypass IPSec issues?
Yes, some environments support SSL VPN or IKEv2 over TLS as alternatives. Check with your IT team before switching to avoid policy violations.
How do I check if certificates are valid?
Use the Windows certificate manager (certmgr.msc) to inspect the certificate chain, expiry dates, and trust status. Ensure the root and intermediate CAs are trusted. Nordvpn Not Working in China Heres Exactly How to Fix It: Quick, Clear Guide for New Zealand Users
What if my DNS still leaks even when connected to VPN?
Force VPN DNS, disable IPv6 if not used, and ensure the resolver is configured to route queries through the VPN tunnel.
How do I test if ports are blocked by a firewall?
Use telnet or PowerShell to test port reachability to the VPN gateway. If ports are blocked, you’ll see connection timeouts or resets.
Is split tunneling safer than full tunnel?
Full tunnel generally provides stronger security by forcing all traffic through the VPN, reducing exposure of sensitive data. Split tunneling can improve performance but may create exposure if not managed correctly.
What’s the best way to document VPN troubleshooting?
Maintain a runbook with common errors, step-by-step fixes, and screenshots of the FortiGate and FortiClient configurations. Include test results and timestamps for reproducibility.
If you found this guide helpful, consider exploring more resources and tools to improve your VPN experience and security posture. For more in-depth help, consult the Fortinet documentation and Windows 11 networking guides, and keep your FortiClient and FortiGate appliances up to date. How to Use NordVPN with Microsoft Edge Your Ultimate Guide
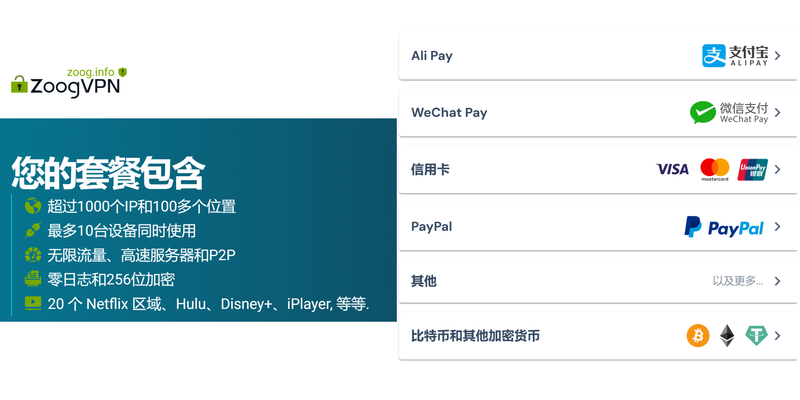
Note: This post includes an affiliate link for privacy-focused browsing tools. If you’re looking to add extra privacy and security while you work, you might consider tools like NordVPN (link: https://go.nordvpn.net/aff_c?offer_id=15&aff_id=132441). This is presented for informational purposes and as an option to support your browsing needs.
Sources:
Nord VPN 在全球的隐私保护与流媒体解锁综合指南:完整评测、设置与比较
Free vpn:全面对比与实用指南,选择最合适的免费VPN方案
苹果手机vpn配置教程与最佳实践:在 iPhone 上选择、设置、优化 VPN 的完整指南
节点订阅地址生成:手把手教你如何制作与管理订阅链接 2026
Ikuvpn: 让VPNH走进日常的安全与隐私新纪元,深度解读和实用指南